In today’s digital world, cybersecurity is more critical than ever. With more users, devices, and data, protecting our digital assets is essential. Cybersecurity covers many areas like application, data, and network security. Implementing robust practices can safeguard businesses, protect data, and ensure quick recovery after breaches. Threats such as malware, ransomware, and phishing are constant challenges, along with evolving dangers and workforce shortages. Best practices include updating software, using strong passwords, multifactor authentication, and staff training. Automation aids threat detection and response. Numerous tools and vendors help defend systems, and career opportunities in cybersecurity are vast. The Department of Homeland Security, under President Biden’s directive, leads the charge in bolstering cybersecurity, addressing threats, and building a skilled, diverse workforce. Secretary Mayorkas has shared his vision for cybersecurity resilience, emphasizing action against rising threats like ransomware and engaging with communities to bolster security awareness.
## Elements of Cybersecurity
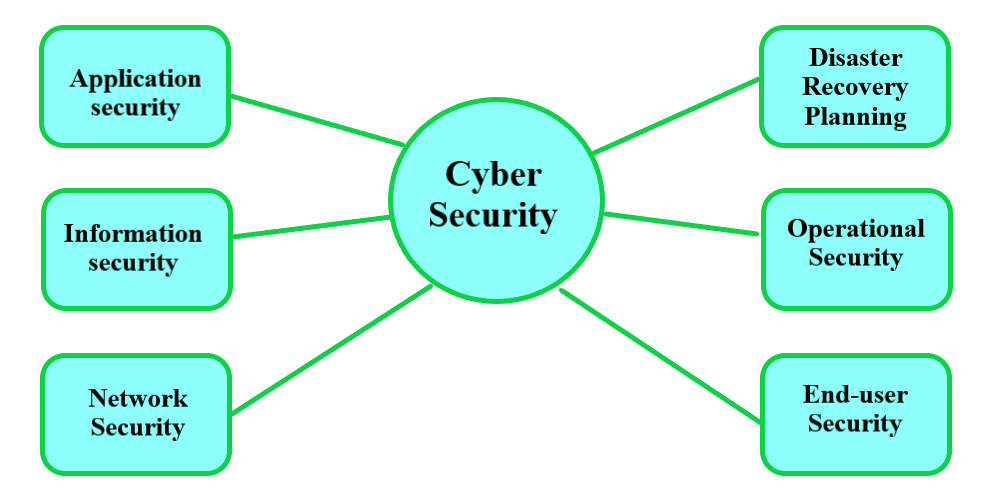
Credits: geeksforgeeks.org
Application security involves the measures taken to **protect applications from threats** that could compromise their integrity. This includes **finding and fixing vulnerabilities** within the software itself, and **ensuring proper access controls** are in place to limit who can do what with your applications. Secure coding practices, regular software updates, and rigorous testing are essential to prevent attacks like SQL injection, cross-site scripting, and other exploitations.
Data security focuses on protecting data from unauthorized access and corruption throughout its lifecycle. Encryption, both at rest and in transit, ensures that data cannot be read by anyone who doesn’t have the right decryption key. Additionally, properly managing user permissions, implementing strong authentication methods, and regularly backing up data are crucial practices to keep information secure. This helps to prevent data breaches, loss, and ensures that data integrity is maintained.
Network security is about safeguarding the underlying networking infrastructure from misuse, malfunction, and unauthorized access. This involves using firewalls, intrusion detection systems, and VPNs to control and monitor network traffic. Regularly updating network hardware and software, along with strict access controls and employing best practices like network segmentation, helps to protect against a variety of threats such as malware, phishing, and distributed denial-of-service attacks. By maintaining a secure network, organizations can ensure the continuity and reliability of their operations.
## Benefits of Implementing Cybersecurity
Implementing **cybersecurity measures is crucial** for business protection. It helps prevent attacks that can lead to financial loss, reputational damage, and legal consequences. By **safeguarding systems and information**, businesses can operate smoothly without disruptive threats.
Cybersecurity is essential for data and network protection. It ensures that sensitive information is kept secure and only accessible to authorized personnel. Effective measures prevent unauthorized access, breaches, and leaks, maintaining the integrity and confidentiality of data.
A strong cybersecurity setup can improve recovery time after an incident. With the right protocols in place, businesses can quickly identify and address security breaches. This **rapid response minimizes downtime** and reduces the impact of attacks, ensuring business continuity.
## Types of Cybersecurity Threats
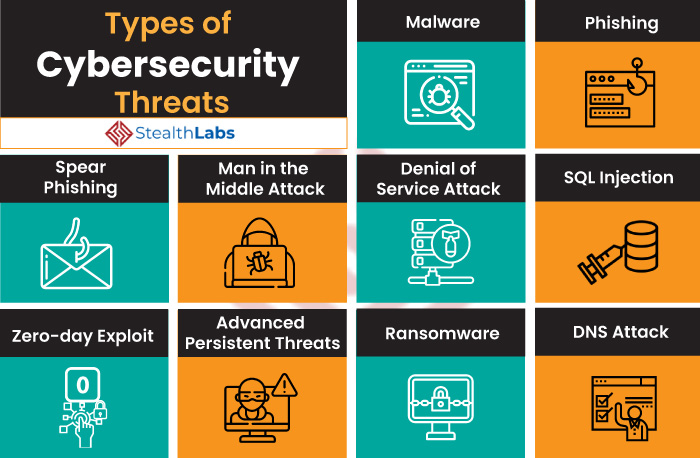
Credits: stealthlabs.com
Malware is a term used to describe malicious software designed to harm, exploit, or otherwise compromise the security of computing devices and networks. It can take many forms, such as viruses, worms, Trojans, and spyware. Some malware is crafted to steal sensitive data, while others might aim to corrupt or delete files. Users can often fall victim to **malware through downloading infected attachments**, visiting compromised websites, or installing unverified software.
Ransomware is a particularly dangerous type of malware that encrypts a victim’s files, rendering them inaccessible. Attackers then **demand a ransom payment**, often in cryptocurrency, in exchange for a decryption key. Ransomware can spread through email attachments, infected software, and websites. Once it gains entry into a system, it can cause significant disruptions to both individuals and organizations, leading to potential financial loss and data breaches.
Phishing is a cyber attack technique where attackers impersonate legitimate entities to deceive individuals into revealing sensitive information, such as usernames, passwords, and credit card numbers. These attacks usually come via fraudulent emails, messages, or websites designed to look genuine. Phishing tactics rely on social engineering to **manipulate victims and exploit** their trust in legitimate institutions. Being aware of the signs of phishing and adopting good cybersecurity practices can help avoid falling prey to these scams.
| Threat Type | Description |
|---|---|
| Malware | Software designed to disrupt, damage, or gain unauthorized access to computer systems. |
| Ransomware | A type of malware that threatens to publish the victim’s data or perpetually block access to it unless a ransom is paid. |
| Phishing | A form of fraud in which an attacker masquerades as a reputable entity or person in email or other communication channels. |
## Top Challenges in Cybersecurity
In the realm of cybersecurity, one of the top challenges is the **constantly evolving threats**. Cybercriminals are always innovating, using more sophisticated methods to breach systems and steal data. This makes it difficult for security measures to keep up, as what works today might not be effective tomorrow. Businesses need to stay alert and constantly update their defenses to counteract these new threats.
Another significant challenge is dealing with the enormous amounts of data generated daily. This **data deluge** makes it difficult for security professionals to monitor and analyze everything effectively. Automated tools can help, but they are not foolproof and can sometimes miss critical threats or generate false alarms. Ensuring the right pieces of data are being scrutinized is crucial for maintaining a strong security posture.
The cybersecurity field also faces a **severe workforce shortage**. There simply aren’t enough qualified professionals to meet the growing demand for cyber defense. This gap leaves many organizations vulnerable, as they struggle to find and retain skilled personnel. Investing in training and education is vital, but it will take time to fill the labor market with the needed expertise.
## Best Practices for Cybersecurity
Keeping your software up to date is crucial for maintaining cybersecurity. Software updates often include patches for security vulnerabilities that could be exploited by attackers. Regular updates ensure that you are protected against the latest threats and that your system runs smoothly with the most current features and performance improvements.
Using strong passwords is fundamental for safeguarding your accounts and personal information. A strong password typically contains a mix of uppercase and lowercase letters, numbers, and special characters. Avoid common words and use a unique password for each of your accounts to reduce the risk of unauthorized access.
Implementing multifactor authentication (MFA) adds an additional layer of security beyond just a password. MFA requires users to provide two or more verification factors, such as something you know (password), something you have (a phone or hardware token), or something you are (fingerprint or other biometrics). This significantly enhances the security of your accounts by making it more challenging for attackers to gain access.
## Role of Automation in Cybersecurity
Automation in cybersecurity is pivotal for **threat detection**. It enables systems to continuously monitor and analyze data for suspicious activities. By using **machine learning and AI**, automated systems can recognize patterns that signify potential threats and flag them for further investigation. This speeds up the identification of risks, allowing for quicker intervention and minimizing damage.
Response automation is equally crucial in the cybersecurity realm. Once a threat is detected, automated systems can initiate predefined responses to thwart attacks. This includes isolating affected systems, deploying patches, and notifying stakeholders. Automating these responses ensures rapid action, reducing the window of opportunity for attackers and mitigating potential harm.
Human augmentation refers to the enhancement of human capabilities through automation. In cybersecurity, this means empowering security professionals with tools that automate routine tasks. By offloading monotonous activities, security experts can focus on more complex issues requiring human insight and expertise. Automation thus acts as a force multiplier, allowing security teams to be more effective and efficient.
## Cybersecurity Vendors and Tools
Vendor solutions in cybersecurity offer a wide range of services designed to **protect against online threats**. These solutions often include comprehensive protection suites that guard against malware, phishing attacks, and other cyber threats. Vendors such as Symantec, McAfee, and Palo Alto Networks provide tools that secure networks, endpoints, and data. Their packages often come with advanced features like threat intelligence, behavior analysis, and automated responses to threats, making it easier for businesses to maintain a secure cyber environment.
Open source tools offer another viable option for maintaining cybersecurity. Many of these tools are highly regarded within the cybersecurity community due to their transparency and the collaborative efforts that go into their development. Options like Wireshark, Metasploit, and Snort provide robust capabilities for network monitoring, vulnerability assessment, and intrusion detection. These tools can be **customized to fit specific needs**, and their open-source nature ensures that they are continually updated with the latest security enhancements.
Cloud-based security tools have become essential as businesses migrate to cloud environments. These tools are designed to protect data stored and processed in the cloud and often offer features like encryption, access control, and continuous monitoring. Solutions from companies like Microsoft Azure, Amazon Web Services, and Google Cloud Platform ensure that **cloud infrastructures are secure** against breaches and other cyber threats. Cloud-based tools also provide scalability and flexibility, allowing businesses to adjust their security measures as their needs evolve.
## Career Opportunities in Cybersecurity
A Chief Information Security Officer (CISO) plays a crucial role in an organization, responsible for **overseeing the entire cybersecurity team** and framework. They develop and implement strategic security measures to protect the company’s data and networks. CISOs also ensure compliance with regulatory requirements and manage cybersecurity risks, making them a key player in maintaining the organization’s secure cyber environment.
Security Engineers design and build systems that protect against cyber threats. They focus on developing tools, implementing security measures, and analyzing security incidents. Their expertise helps in creating robust defenses against potential attacks, ensuring that the organization remains secure from evolving cyber threats. Security Engineers also conduct vulnerability assessments and work closely with other IT professionals to **enhance the overall security** posture.
Security Analysts are on the frontline of defending against cyber threats. They monitor network traffic, analyze security breaches, and **respond to incidents**. By evaluating the effectiveness of current security measures and recommending improvements, they ensure the organization stays one step ahead of cyber attackers. Security Analysts also keep up with the latest trends and threats in the cybersecurity landscape, making their role critical in maintaining a secure cyber environment.
## Educational Requirements for Cybersecurity Roles
For entry-level positions in cybersecurity, typically an associate’s degree or a bachelor’s degree in computer science, information technology, or a related field is required. Certifications such as CompTIA Security+ or Certified Information Systems Security Professional (CISSP) can also be beneficial. Hands-on experience through internships or lab work is highly valued by employers for these roles.
Mid-level positions generally require a bachelor’s degree plus several years of experience in the field. Advanced certifications such as Certified Information Systems Auditor (CISA), Certified Ethical Hacker (CEH), or Certified Information Security Manager (CISM) are often sought after. These roles might include positions like security analyst or network security engineer, and require a deep understanding of cybersecurity principles and practical implementation.
Senior-level positions often demand a **master’s degree in cybersecurity** or related disciplines, along with extensive experience. Professionals at this level might hold certifications such as CISSP, CISM, or GIAC Security Expert (GSE). These roles, which could include Chief Information Security Officer (CISO) or Director of Information Security, require strategic oversight and the ability to lead large teams and manage complex security frameworks.
## Government Efforts in Cybersecurity
The Department of Homeland Security (DHS) has been leading efforts to enhance cybersecurity across federal, state, and local governments, as well as the private sector. DHS aims to protect critical infrastructure and ensure a secure cyber environment. Initiatives like the Cybersecurity and Infrastructure Security Agency (CISA) have been pivotal in **addressing emerging threats** and collaborating with stakeholders to improve cyber resilience.
President Biden has made cybersecurity a top priority, with a focus on strengthening the country’s defenses against cyber threats. His administration has emphasized the need for robust national policies, greater investments in cybersecurity technologies, and enhanced cooperation with international allies. Executive orders and federal directives are part of this comprehensive strategy to safeguard America’s digital infrastructure from sophisticated cyber attacks.
Secretary Mayorkas has outlined his vision for cybersecurity resilience through a series of measures aimed at improving the nation’s cyber posture. His approach includes increasing funding for cybersecurity programs, fostering **public-private partnerships**, and promoting a culture of cyber hygiene. By prioritizing resilience, Mayorkas hopes to ensure that the nation’s critical systems can withstand and quickly recover from cyber incidents.
## Frequently Asked Questions
#### 1. What is cyber security and why is it important?
Cyber security is about protecting computers, networks, and data from attacks or unauthorized access. It’s important because it helps keep personal information safe, ensures businesses can operate smoothly, and protects against financial loss.
#### 2. What are the most common types of cyber threats?
Common cyber threats include viruses, malware, phishing attacks, ransomware, and hacking. These threats can steal information, damage systems, or lock you out of your data.
#### 3. How can I protect my computer from viruses and malware?
You can protect your computer by installing antivirus software, keeping your system updated, being cautious with email attachments and downloads, and using strong, unique passwords.
#### 4. What should I do if I think my personal data has been hacked?
If you think your personal data has been hacked, you should change your passwords immediately, notify your bank or credit card company, and monitor your accounts for unusual activity. You may also want to inform the authorities.
#### 5. Why do companies need a cyber security policy?
Companies need a cyber security policy to set guidelines on how to protect sensitive information, respond to cyber threats, and ensure employees follow best practices. This helps prevent data breaches and protects the company’s reputation.
TL;DR Cybersecurity encompasses various elements such as application, data, and network security. Its benefits include business protection and improved recovery time. Threats include malware, ransomware, and phishing. Challenges involve evolving threats, data deluge, and workforce shortages. Best practices include keeping software updated, using strong passwords, and implementing multifactor authentication. Automation in cybersecurity enhances threat detection and response. Cybersecurity vendors and tools range from vendor solutions to open-source and cloud-based tools. Career opportunities vary from entry-level to senior positions such as Chief Information Security Officer. Educational requirements differ by role. Government efforts include leadership by the Department of Homeland Security and President Biden’s and Secretary Mayorkas’ priorities.