In today’s digital jungle, verifying an email sender’s identity is as crucial as knowing which mushrooms are edible. First, always check the actual email address instead of falling for fancy display names, scammers are crafty! Next up, inspect those domains: a sneaky “netf1ix” might just steal your Netflix password. Don’t forget to analyze email headers; they’re like ancient scrolls revealing all mysterious origins. Incorporate DMARC and SPF protocols to prevent impersonation while employing filtering solutions powered by AI to catch unwanted guests before they arrive. Train your team about the dangers of phishing and encourage vigilance, because one careless click can lead to chaos!
Table of Contents
- Inspect Sender Domains
- Analyze Email Headers
- Use Email Verification Services
- Train Your Team on Email Safety
- Implement Magic Links and OTPs
- Use OAuth and SSO for Secure Logins
- Challenges in Verifying Sender Identity
- Frequently Asked Questions
3. Inspect Sender Domains
 Credits: emailonacid.com
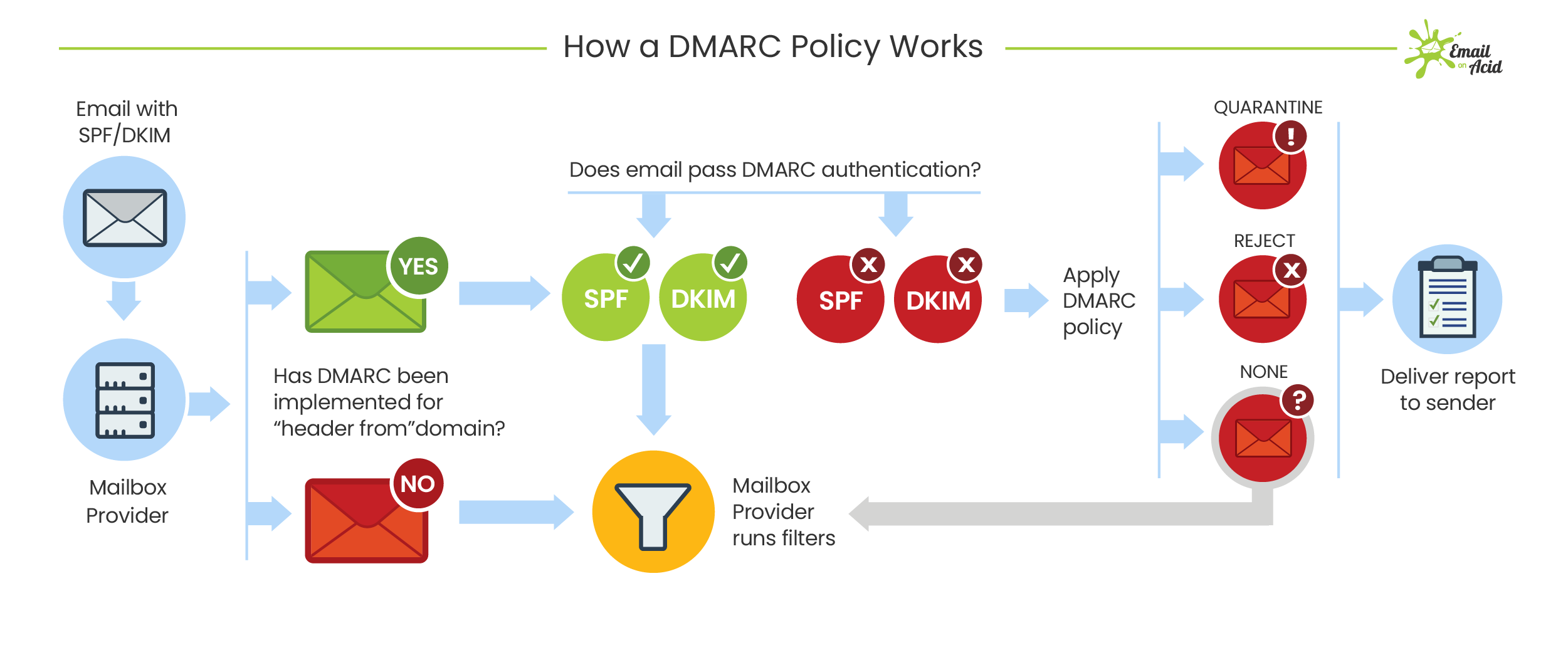
Credits: emailonacid.com
Inspecting sender domains is like the bouncer checking IDs at a bar: you want to ensure that the email you’re dealing with is of legal age (and truly legit). The domain is the soul of the email, so if it doesn’t look right, toss it aside like a rotten tomato! Be wary of lookalike domains, they’re the sneaky imposters at a costume party, hoping to blend in with the crowd. A quick Google search can reveal if a domain has a history of scams, so don’t skip it!
When you check the sender domain, make sure it aligns with the company’s branding. If it seems a little off, trust your gut: if something feels fishy about the domain, it probably is. And don’t forget to look for HTTPS in the sender’s website link; if it’s missing, that’s a big red flag. Scammers often set up shop with new domains that vanish as quickly as they appear, so if the domain seems fresh off the press, proceed with caution. Remember, a legitimate domain has a track record, if you haven’t heard of it, it’s time to be suspicious! Your email security is worth a little snooping.
- The domain is the soul of the email. If it’s not right, toss it aside like a rotten tomato!
- Watch out for lookalike domains, they’re like imposters at a costume party, trying to blend in with the crowd.
- Legitimate domains have a history. If you haven’t heard of it, be cautious!
- Checking the sender domain is like checking ID at a bar: you want to make sure they’re of age (and legit).
- A quick Google search can reveal if a domain is known for scams. Don’t skip it!
- Look for HTTPS in the sender’s website link. If it’s missing, that’s a sign to be skeptical.
- If the domain seems new, question it. Scammers often set up shop for a short time and then vanish!
- Make sure the domain aligns with the company’s branding. If it looks off, it probably is.
- Your gut feeling matters here. If something feels fishy about the domain, trust that feeling!
4. Analyze Email Headers
Email headers are like the backstage pass of the email world, revealing the secrets of where that email came from and who sent it. If you’re curious about an email’s origin story, the header is where the magic happens. With a little practice, you can learn to read these headers, which is like cracking a secret code that could save you from phishing attacks.
When you look at email headers, pay attention to the ‘Received’ lines, they’re like the footprints left behind by an email, showing you the route it took to reach your inbox. If the header looks like a jumbled mess, that’s a big red flag. Scammers often try to hide their tracks, so be cautious.
Headers can also reveal if the email passed important checks like SPF and DKIM. Think of these checks as a safety net for your inbox. If the email doesn’t pass these checks, toss it in the digital trash! And if you find discrepancies in the header, trust your instincts, something’s off.
To make header analysis easier, consider using header analysis tools. They’re like GPS for navigating the email jungle, guiding you through the maze of information. By becoming a header detective, you can better protect your business from the perils of email fraud.
10. Use Email Verification Services
Email verification services are like your inbox’s trusty sidekick, always on the lookout for those sneaky fakes! Imagine having a digital bouncer that only lets the good emails in, keeping your list clean and your reputation intact. Tools like NeverBounce or ZeroBounce are fantastic options, they check if an email can actually receive messages without sending them. It’s basically like peeking inside the mailbox without the risk of getting your hand stuck! By using these services, you significantly reduce the risk of spam complaints and improve your open rates because, let’s face it, everyone loves getting mail from verified sources. Regularly cleaning up your email list is crucial, especially for businesses that rely on email marketing. Investing in these verification tools pays off in the long run, saving you time and those pesky headaches caused by bounced messages. So, don’t let invalid emails clutter your list, give them the boot and keep your email game strong!
| Service Name | Features | Benefits |
|---|---|---|
| NeverBounce | Real-time email validation, bulk verification, integrations with CRM tools | Reduces bounce rates, improves open rates, ensures messages reach the inbox |
| ZeroBounce | Email appending, API access, email scoring | Identifies invalid emails, enhances marketing lists, provides detailed analytics |
| Mailgun | Real-time verification, pre-send validation, extensive reporting | Prevents spam complaints, protects sender reputation, boosts deliverability |
11. Train Your Team on Email Safety
Training your team on email safety is like teaching them to dodge digital landmines, but with a lot more laughter involved. Regular training sessions can turn a mundane topic into an exciting opportunity to learn about the sneaky world of phishing and email fraud. Why not spice things up with fun quizzes or interactive scenarios? Imagine your colleagues trying to spot a suspicious email while racing against the clock, who doesn’t love a little friendly competition?
Real-life examples of phishing scams can be eye-opening, especially when you sprinkle in a funny story or two to keep everyone engaged. This way, employees not only learn to recognize red flags but also remember the lesson more vividly. Encouraging your team to report suspicious emails to the IT department can foster a culture of vigilance, and consider rewarding those who do. Who wouldn’t want a little treat for being a digital detective?
Creating a handy checklist for employees can make verifying email requests feel like a treasure hunt, complete with a map and a chance for glory. Role-playing exercises can also be a hit, allowing employees to practice responding to phishing attempts. Bonus points if they come in costume!
An internal email safety newsletter can keep everyone informed about the latest threats and tips, filled with hilarious cartoons or memes that make learning about security a lot more fun. Implementing a buddy system where employees can double-check emails with a colleague before taking action adds another layer of security, because two heads are indeed better than one.
Finally, remember that training should be ongoing. New phishing schemes pop up faster than you can say “urgent request!” So, keep everyone on their toes and encourage a culture where asking questions about emails is not just welcomed, but celebrated. No one should feel silly for double-checking before they click!
12. Implement Magic Links and OTPs
Magic links are like the fairy godmothers of email security, granting instant access without the hassle of remembering passwords. When users click on a magic link, they feel like they’ve just been given a VIP pass to the email party, no bouncers allowed! Pairing magic links with One-Time Passwords (OTPs) is like adding a secret handshake that only the right people know. Make sure those OTPs expire quickly, so they’re as fleeting as a good punchline in a comedy show. Encourage users to set up two-factor authentication for even more peace of mind, because who doesn’t love a little extra security? Sending OTPs via SMS or email gives users the thrill of choosing their preferred delivery method, much like selecting pizza toppings! Don’t forget to explain to users how magic links and OTPs work, so they understand they’re not just magical unicorns appearing out of nowhere. A humorous tagline in your communications, like ‘No magic wand needed, just a click!’ can keep things light-hearted. Also, have a backup recovery option for users who misplace their magic link or OTP, because even the best wizards can have an off day. Regularly review how these methods are performing, ensuring they work like a well-oiled machine, or at least a semi-functioning one!
13. Use OAuth and SSO for Secure Logins
Using OAuth and Single Sign-On (SSO) is like having an exclusive VIP pass at the login party. Instead of juggling a dozen passwords like a circus performer, your users can waltz in with just one! By allowing them to use trusted third-party logins like Google or Microsoft, they can confidently stroll into your site, knowing that these big names are backing them up like a loyal bodyguard. OAuth works to keep their data safe, almost like having a digital security detail at their virtual door. Plus, SSO can help rescue them from password fatigue, saving them from the endless cycle of resets that can feel like a cruel joke. Who wants to remember 12 passwords when they can just recall their favorite ice cream flavor instead?
And let’s not forget the joy of logging in with a single click, it’s like finding that perfect parking spot right in front of the venue! To get started, provide clear instructions on setting up and using OAuth and SSO, because a little guidance goes a long way. Encourage your users to add multifactor authentication for that extra layer of security, which is like adding more layers than a good lasagna. Keep track of user feedback on these features, just like a comedian gauging laughs to fine-tune their routine. And remember, regularly updating your security protocols is essential to stay ahead of any potential threats, much like a comedian refreshing their material to keep the audience engaged. So, let your users enjoy the convenience and security that OAuth and SSO offer, making their login experience smooth and worry-free!
14. Challenges in Verifying Sender Identity
Verifying sender identity is like trying to catch a magician’s trick, one minute it looks real, and the next, it’s all smoke and mirrors. Exact-domain spoofing is a classic example; these sneaky attackers make emails appear as if they’re coming from legitimate sources, leaving you questioning your own judgment. Then we have lookalike domains, the impersonators of the internet, like that one comedian who just can’t get the timing right. They change a letter or two, and suddenly you’re looking at support@netf1ix.com instead of support@netflix.com. Talk about a bad stand-up act!
But wait, there’s more! User behavior plays a huge role here too. In the heat of the moment, people might click ‘yes’ on a pop-up ad just like they laugh at a joke that’s not funny. Phishing attackers are sharpening their skills, so verification methods must always keep pace, like a great punchline that catches everyone off guard. It’s essential to educate users about these challenges, think of it as giving them the tools to become savvy email ninjas.
Encouraging users to scrutinize sender details is crucial; it’s like checking IDs at the door of a comedy club. If it feels off, it probably is, much like that comedian who just doesn’t vibe with the audience. Creating a ‘red flags’ list could help users spot email con artists trying to crash the party. And let’s not forget the role of technology in this high-stakes showdown. Advanced filtering solutions and AI analysis are like the superheroes of email security, swooping in to save the day. Regularly updating training materials is key, much like a comedian tweaking their set to stay relevant. In this ever-evolving landscape, staying sharp is your best defense against the email tricksters.
Frequently Asked Questions
What is email sender verification and why does it matter?
Email sender verification is like a bouncer for your inbox, making sure that the person trying to get in really is who they say they are. It matters because you don’t want your inbox filled with spam or phishing attempts, right? It’s all about keeping it classy in the digital world.
How can I tell if an email is fake or from a real sender?
Think of it like detective work! Look at the sender’s email address, check for weird spelling or odd domains, and watch out for those pesky grammar mistakes. If it seems too good to be true or feels fishy, there’s a good chance it’s a catfish in your inbox.
What tools can I use to verify email sender identities?
There are plenty of digital tools out there, like email verification services, tracking links, and even good ol’ reverse email lookup sites. They help you sniff out the fakes and confirm if that ‘Nigerian prince’ is actually a prince or just a prankster.
Can I find out if an email sender has a bad reputation?
Absolutely! You can use tools like reputation checkers or spam databases. It’s like checking Yelp reviews before trying out a new restaurant, don’t want to end up with a bad meal, or in this case, a bad email!
What should I do if I suspect an email sender is not legitimate?
First, don’t open any links or attachments. That’s like inviting a raccoon into your home. Report it as spam, block the sender, and tell your colleagues, it’s always good to spread awareness. Safety in numbers, right?
TL;DR Want to keep your business safe from sneaky email scams? First, check the actual email address, not just the flashy display name. Then, inspect sender domains, make sure they match up or you might be getting punked. Next, dive into those email headers for some not-so-secret intel, and implement some fancy tech like DMARC and SPF. Don’t forget to use email verification services, train your team to spot suspicious emails, and consider using magic links or OTPs for logins. The challenges are real, like spoofing and lookalike domains, but with a mix of tech and a vigilant team, you can outsmart the bad guys!